Researchers have uncovered a rash of ongoing attacks designed to damage routers and other Internet-connected appliances so badly that they become effectively inoperable.
PDoS attack bots (short for “permanent denial-of-service”) scan the Internet for Linux-based routers, bridges, or similar Internet-connected devices that require only factory-default passwords to grant remote administrator access. Once the bots find a vulnerable target, they run a series of highly debilitating commands that wipe all the files stored on the device, corrupt the device’s storage, and sever its Internet connection. Given the cost and time required to repair the damage, the device is effectively destroyed, or bricked, from the perspective of the typical consumer.
Over a four-day span last month, researchers from security firm Radware detected roughly 2,250 PDoS attempts on devices they made available in a specially constructed honeypot. The attacks came from two separate botnets—dubbed BrickerBot.1 and BrickerBot.2—with nodes for the first located all around the world. BrickerBot.1 eventually went silent, but even now the more destructive BrickerBot.2 attempts a log-on to one of the Radware-operated honeypot devices roughly once every two hours. The bots brick real-world devices that have the telnet protocol enabled and are protected by default passwords, with no clear sign to the owner of what happened or why.
Move over, Mirai
The attacks are a variation on those mounted by Mirai, a botnet made up of network cameras, digital video recorders, and other so-called Internet-of-things devices. The point of Mirai is to build an army of devices that cripple prominent websites with record-setting distributed DoS attacks. The motivation for the PDoS attacks remains unclear, in part because BrickerBot.2 attacked a much wider variety of storage devices—including those used by servers—rather than storage used only by more limited IoT devices.
“When I discovered the first BrickerBot, I thought it was a drastic attempt to stop the IoT Botnet DDoS threat,” Radware researcher Pascal Geenens told Ars. “I thought this was a competitor hacker who wanted to take out his competition and get access to the list of IP [addresses] of bots that were in the competitor’s botnet. But upon discovery of the second BrickerBot this theory changed, as the second one is targeting any Linux-based system—not only embedded, BusyBox-based Linux with flash storage. What motivates people to randomly destroy things? Anger, maybe? A troll, maybe?”
All of the devices targeted by BrickerBot.1 ran the BusyBox collection of Unix tools, exposed a secure shell command window to the open Internet, and ran an older version of the Dropbear SSH server. Most of the destructive effects of BrickerBot.1 resulted from targeting two specific types of flash storage—Memory Technology Device and MultiMediaCard devices—which are widely used by IoT devices and also found in Raspberry Pi mini computers. During a four-day period starting on March 20, BrickerBot.1 used nodes scattered all over the world to attack devices inside the Radware honeypot 1,895 times. The devices performing the attack were access points and wireless bridges made by Ubiquiti Networks, with operating environments that were similar to the devices on the receiving end of the attack.
Meaner, stealthier BrickerBot.2 emerges
Less than an hour after BrickerBot.1 began attacking the Radware honeypot devices, BickerBot.2 made its first appearance. BrickerBot.2 targets a much wider variety of storage disks, and many of the Linux-based devices they’re found on don’t run BusyBox or use the Dropbear SSH server. BrickerBot.2 also uses the Tor anonymity service to conceal the IP addresses of its member nodes. Still, BrickerBot.2 can only access machines that expose a telnet service protected by default passwords—a requirement that greatly limits its destructive effects.
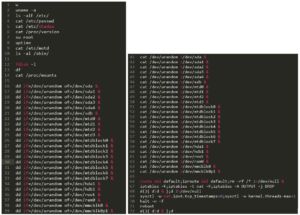
The updated botnet also carries out a longer list of malicious commands once it successfully gains administrative control of a targeted device. As the image above shows, in addition to corrupting the storage device, BrickerBot.2 wipes all stored files, removes the default Internet gateway, disables TCP timestamps, and limits the maximum number of kernel threads to just one. That all but ensures that most damaged devices won’t be restored without a major undertaking. Radware has more details about the attacks here.
The common thread linking all the devices—whether targeted by BrickerBot.1 or BrickerBot.2—is that they are so poorly secured that they are easy prey for Mirai and other highly destructive botnets. That leaves open the possibility that the rash of PDoS attacks is being carried out by one or more vigilantes who want to take out these devices before they can be conscripted into a powerful DoS army that poses a serious threat to the Internet as we know it. IoT users who don’t want to change default passwords and close or limit access to telnet and SSH out of concern they’ll be used in crippling attacks against others now have a much more self-interested reason for locking down their devices—preventing them from being bricked.